 Definition
Definition

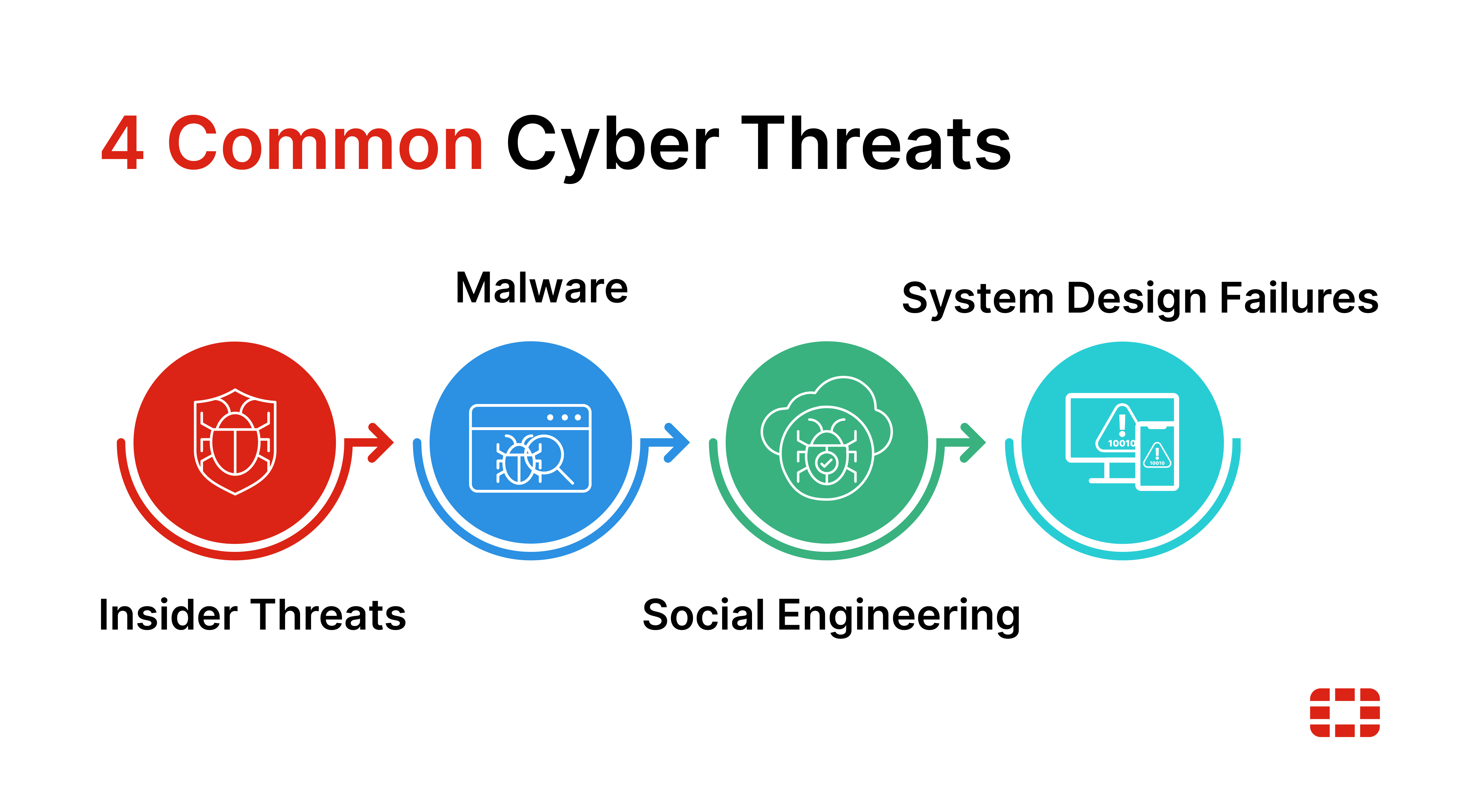
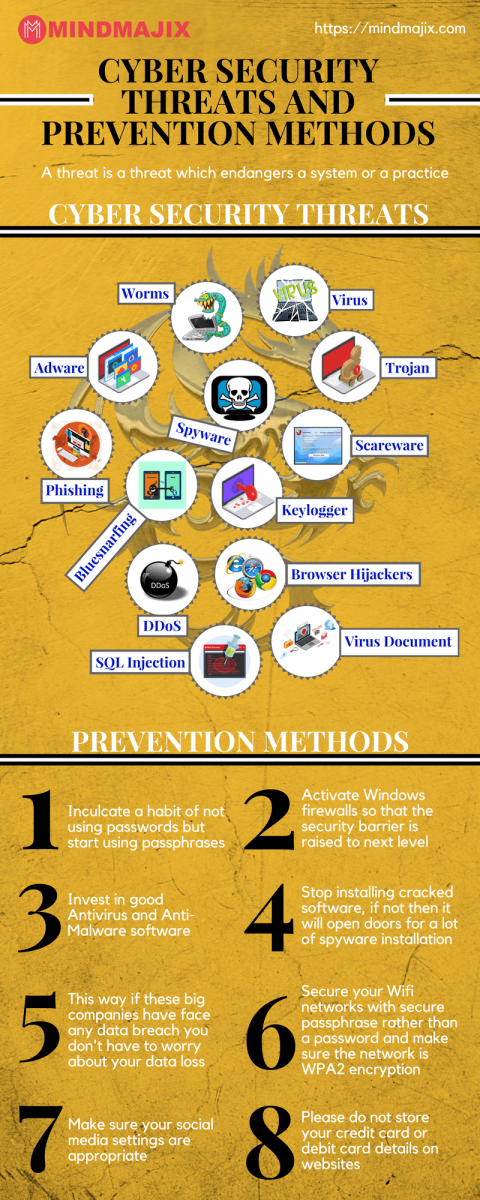
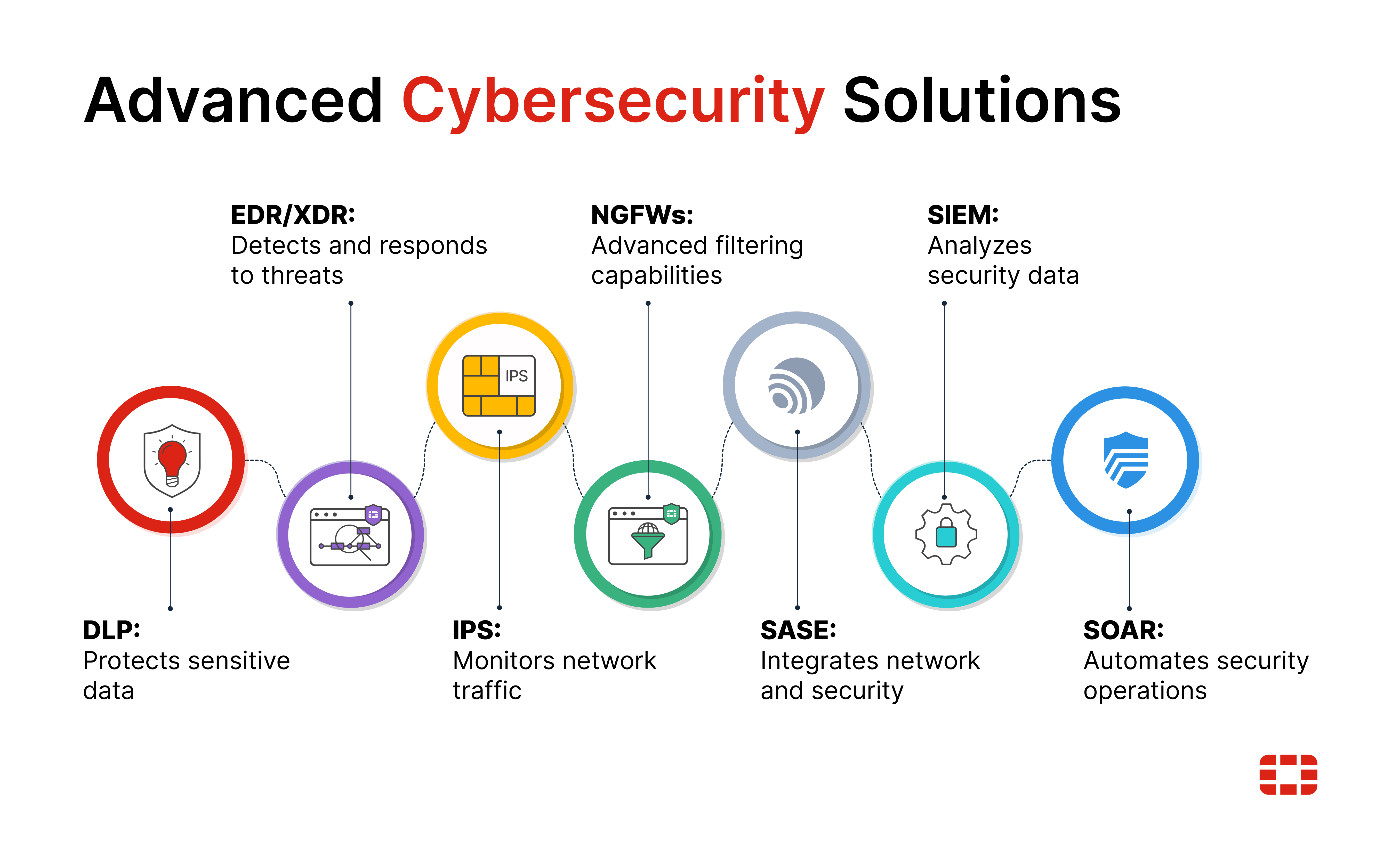
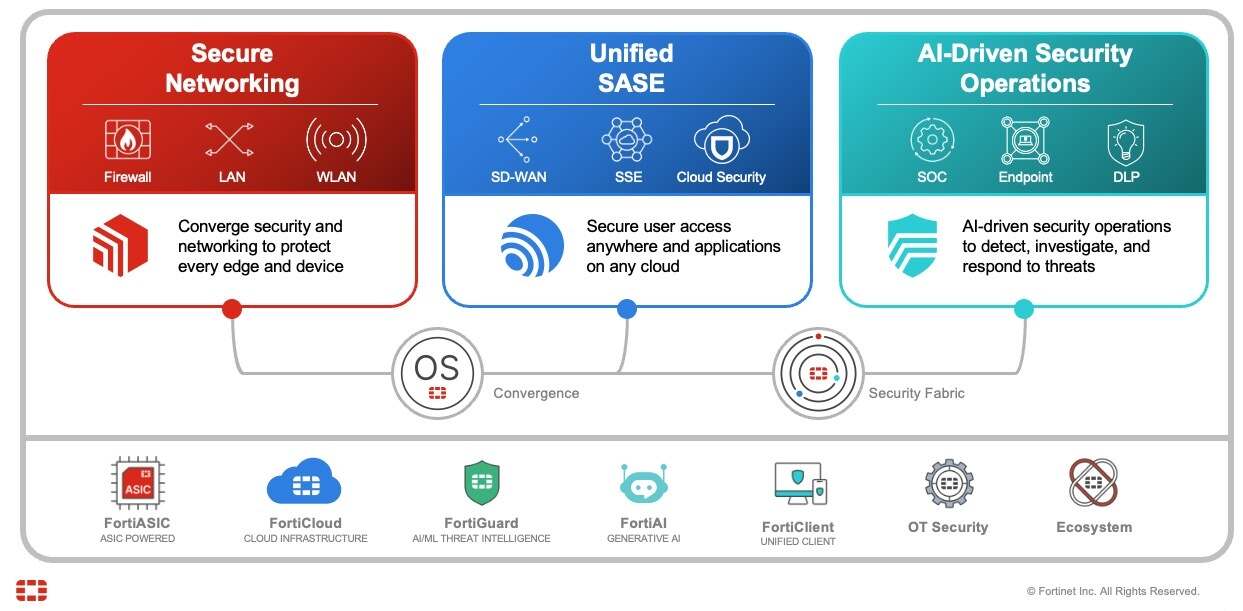
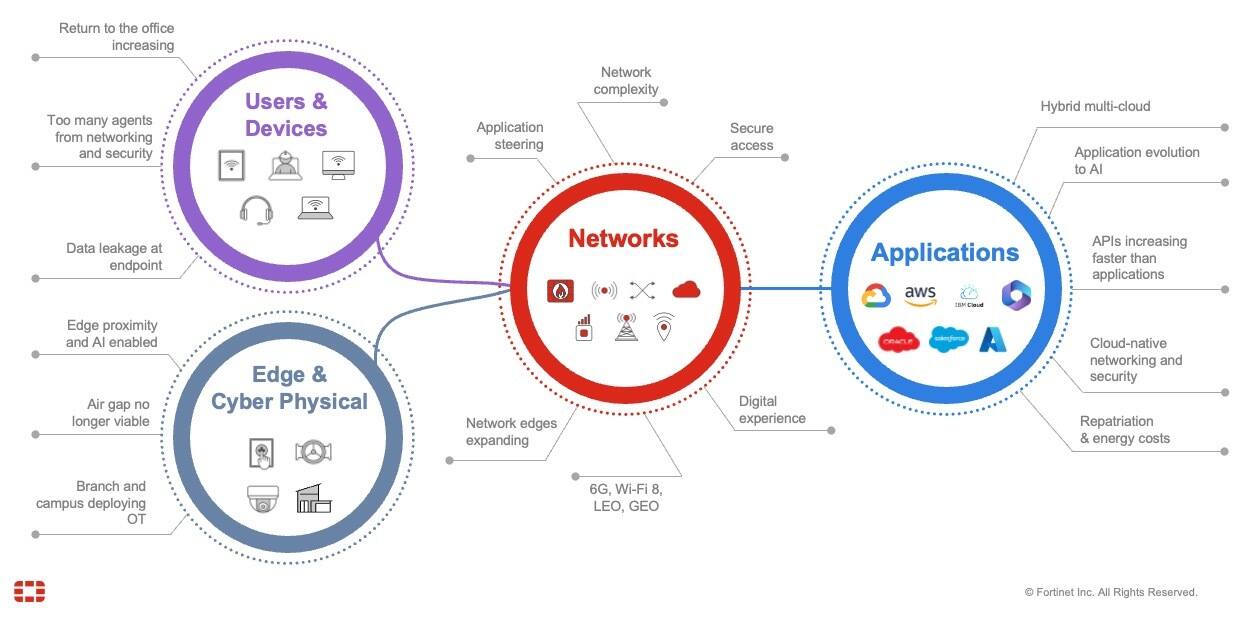
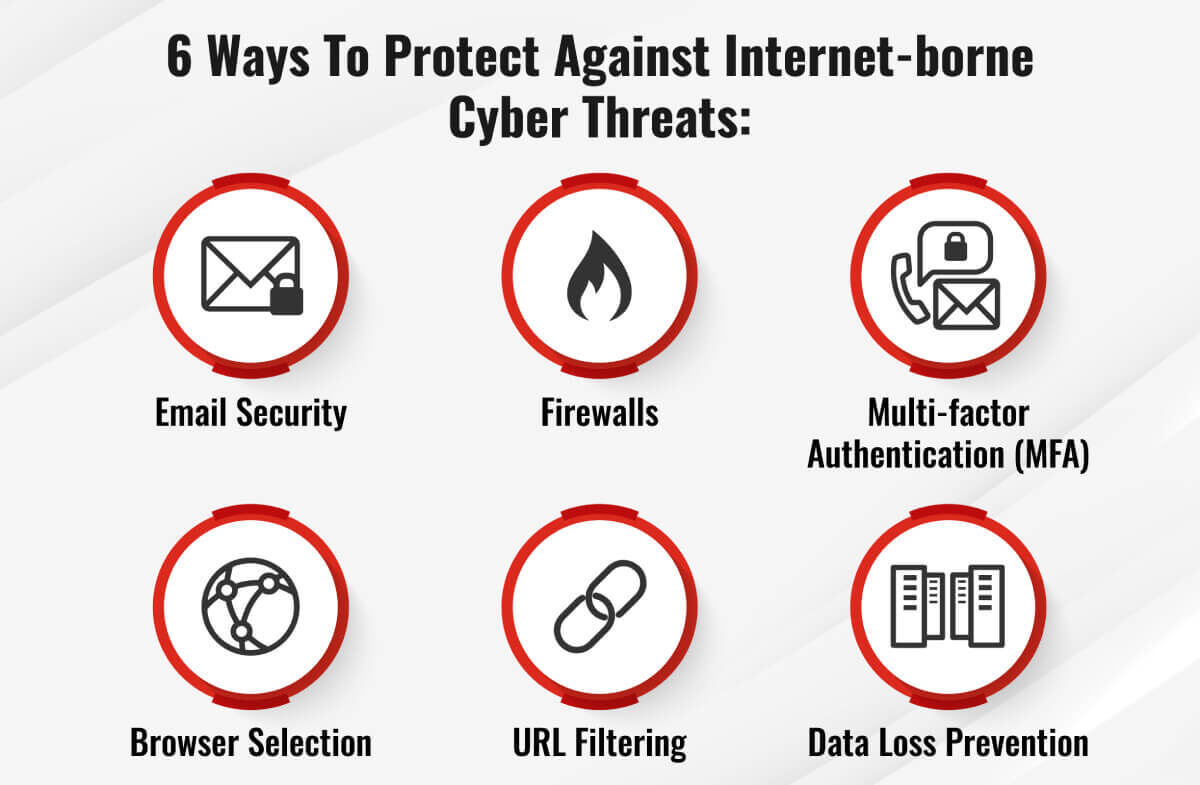
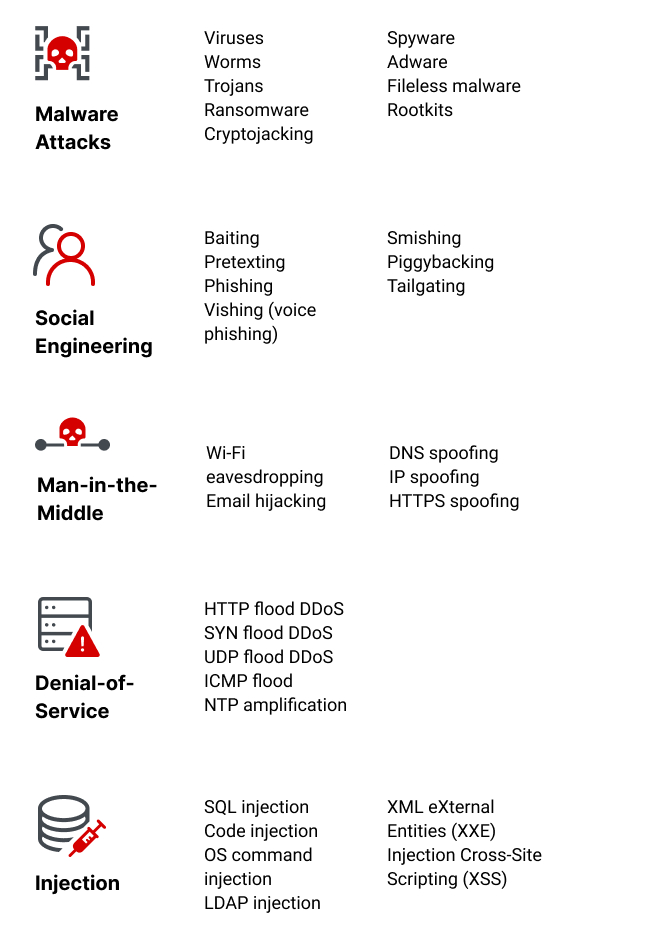
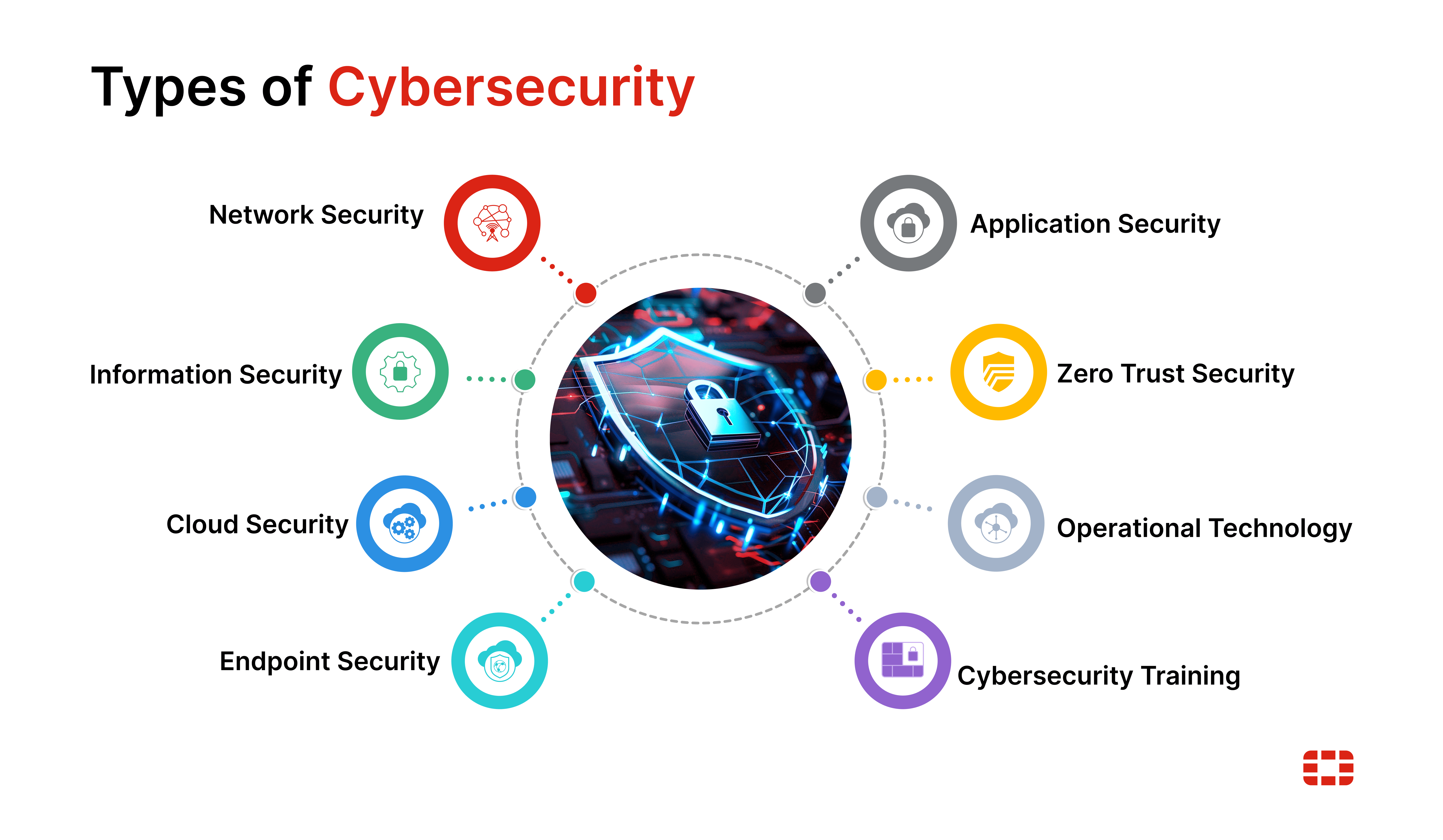
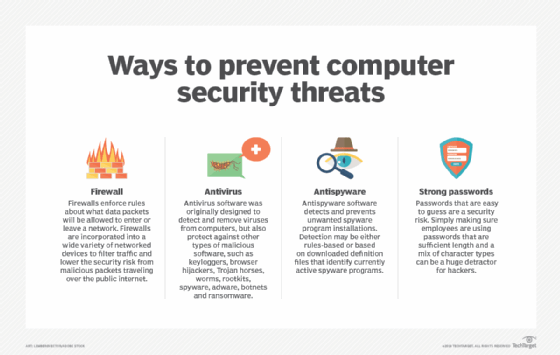
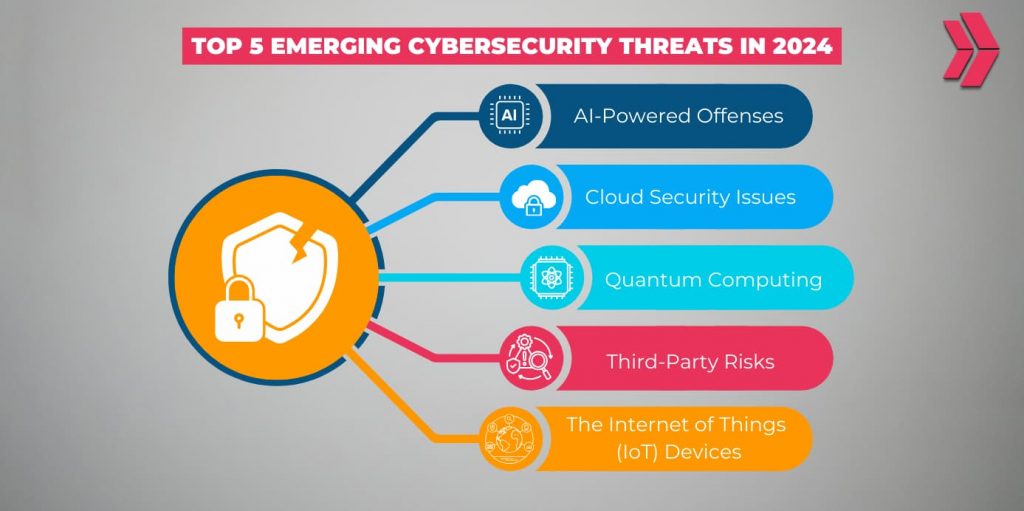
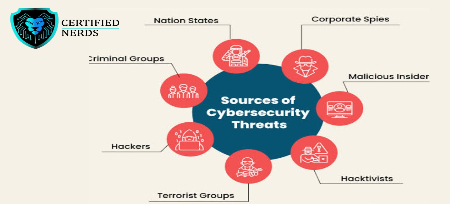
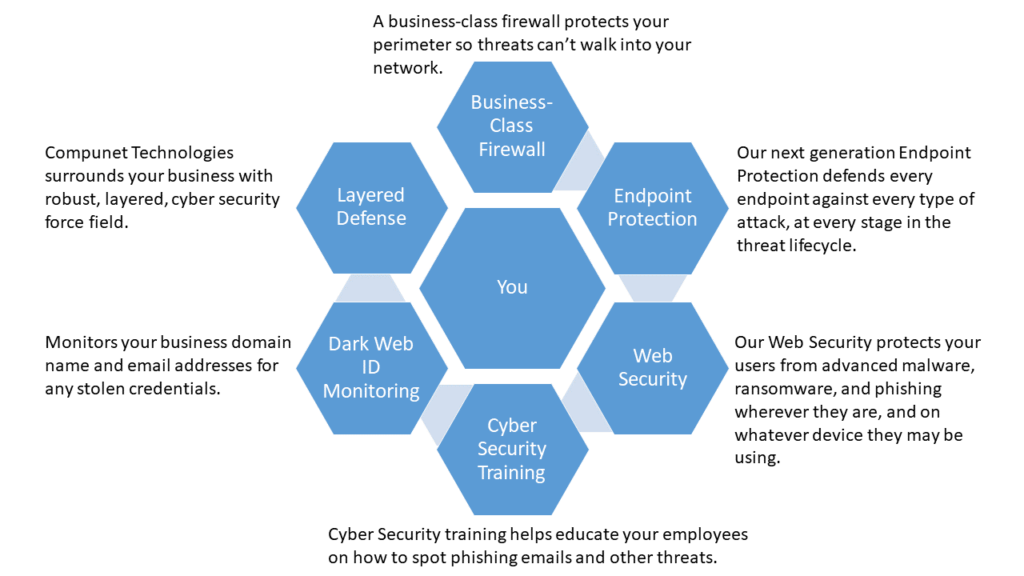
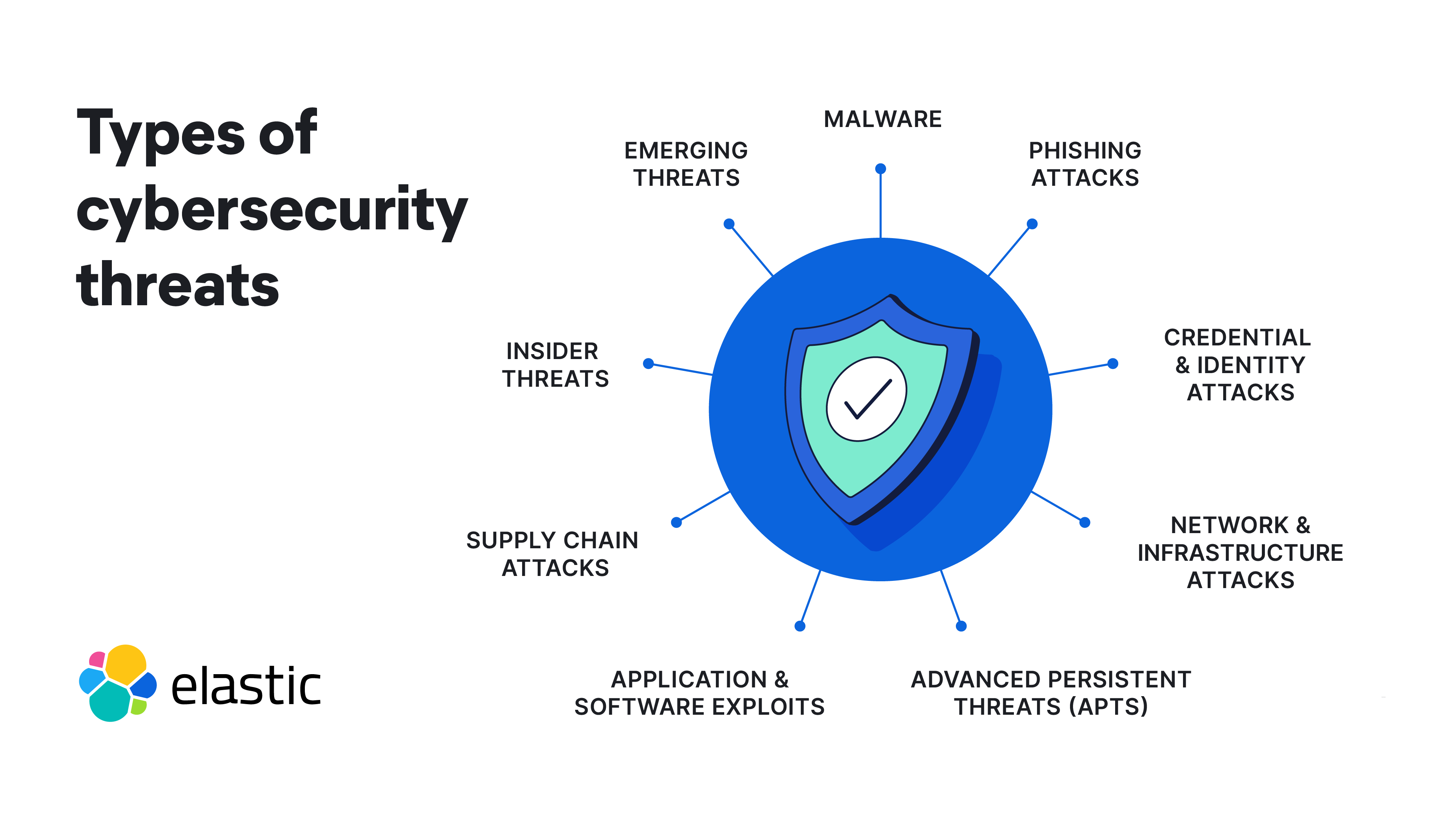
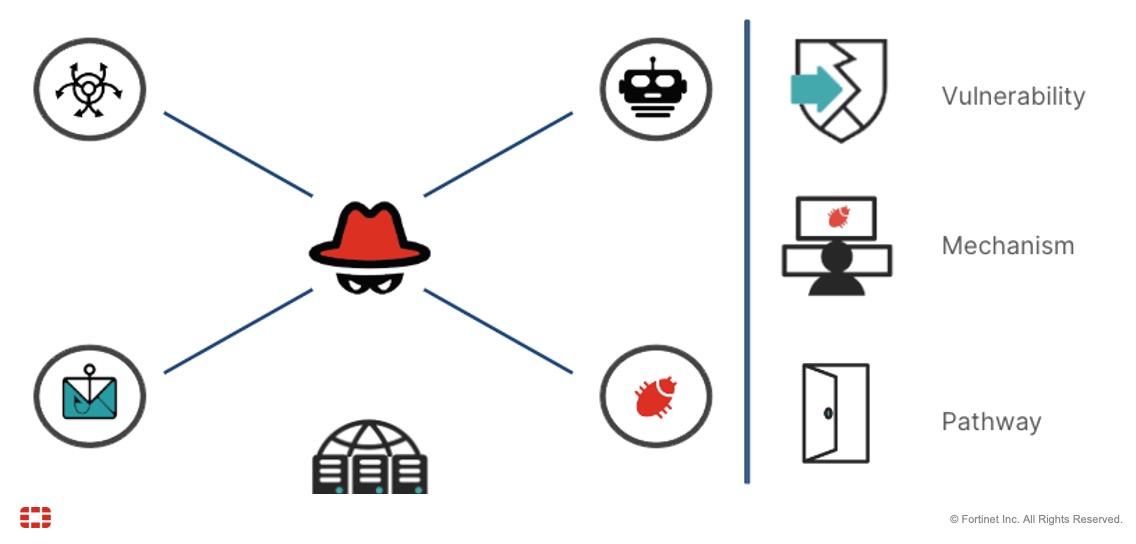
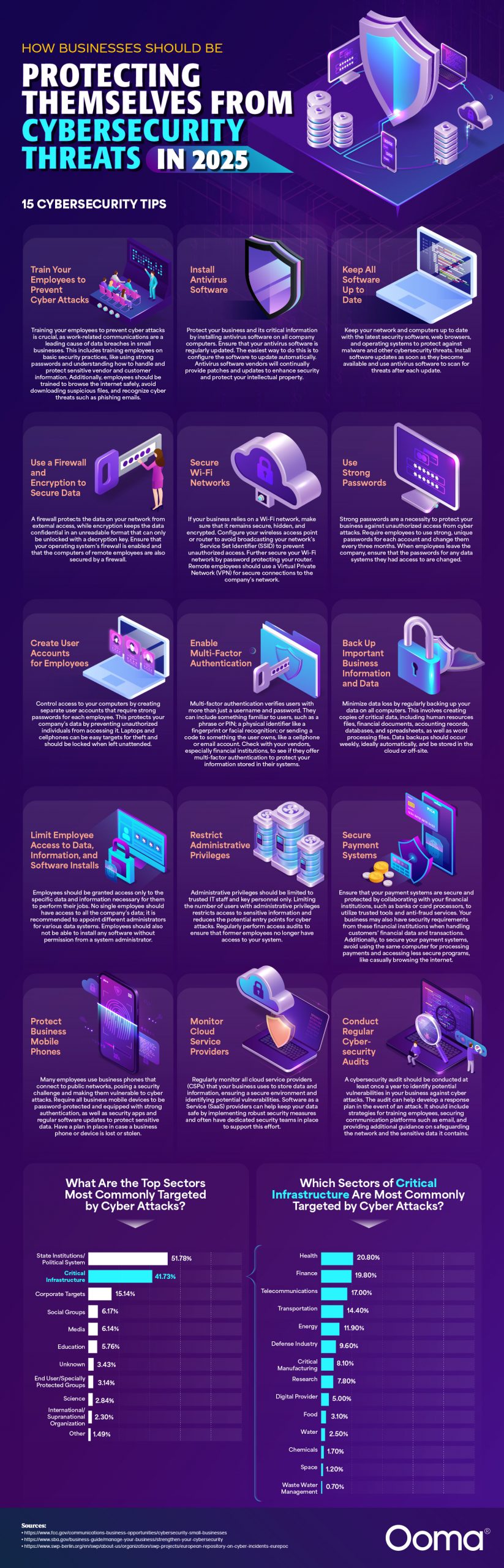
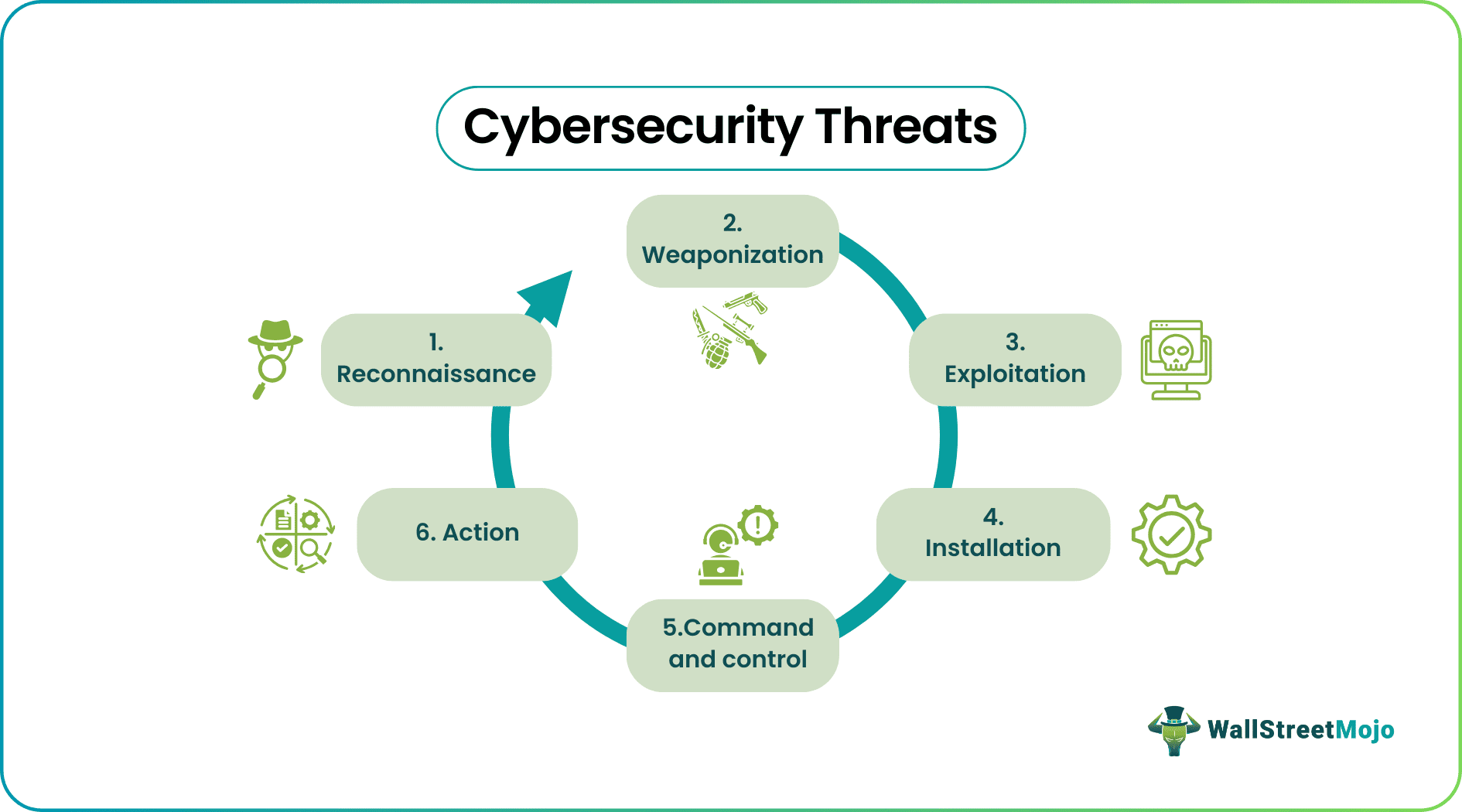
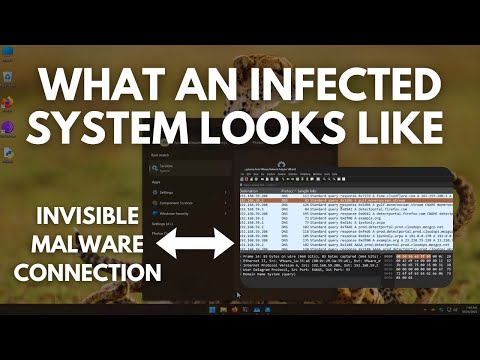
Cybersecurity threats refer to malicious activities that compromise computer systems, networks, or data, such as hacking, phishing, and malware attacks Threats can come from internal sources, like employees with malicious intent, or external sources, like cybercriminals and nation-state actors Types of cybersecurity threats include viruses, worms, Trojans, spyware, adware, and ransomware, which can cause data breaches, system crashes, and financial losses Prevention strategies include installing antivirus software, keeping systems and software up to date, using strong passwords and multi-factor authentication, and implementing firewalls and intrusion detection systems Network segmentation and access controls help limit the spread of threats, while regular backups and disaster recovery plans ensure business continuity in case of an attack Employee education and awareness are crucial in preventing social engineering attacks, such as phishing emails and pretexting schemes, which can trick users into divulging sensitive information Regular security audits and penetration testing help identify vulnerabilities and weaknesses, allowing for swift remediation and mitigation of potential threats
 Images
Images

































 Videos
Videos








 Articles
Articles  Shopping
Shopping 


















 Media Sources
Media Sources 



















