 Definition
Definition

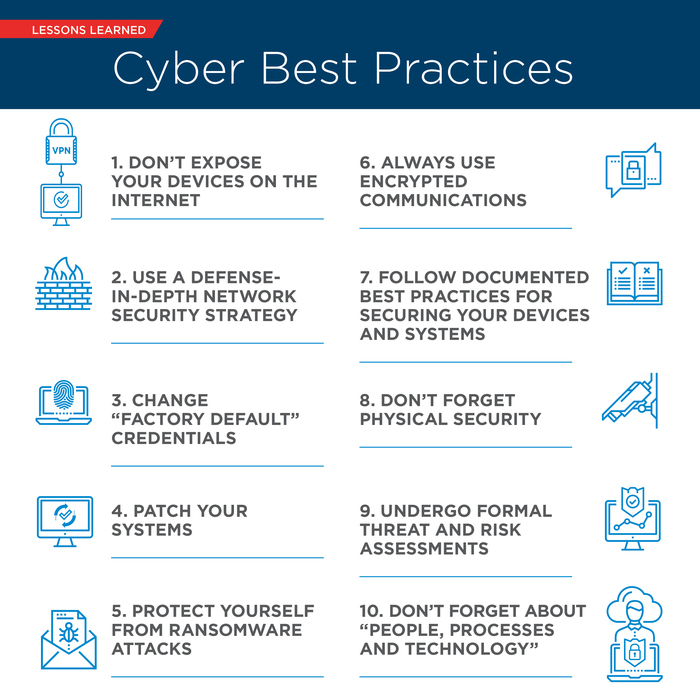
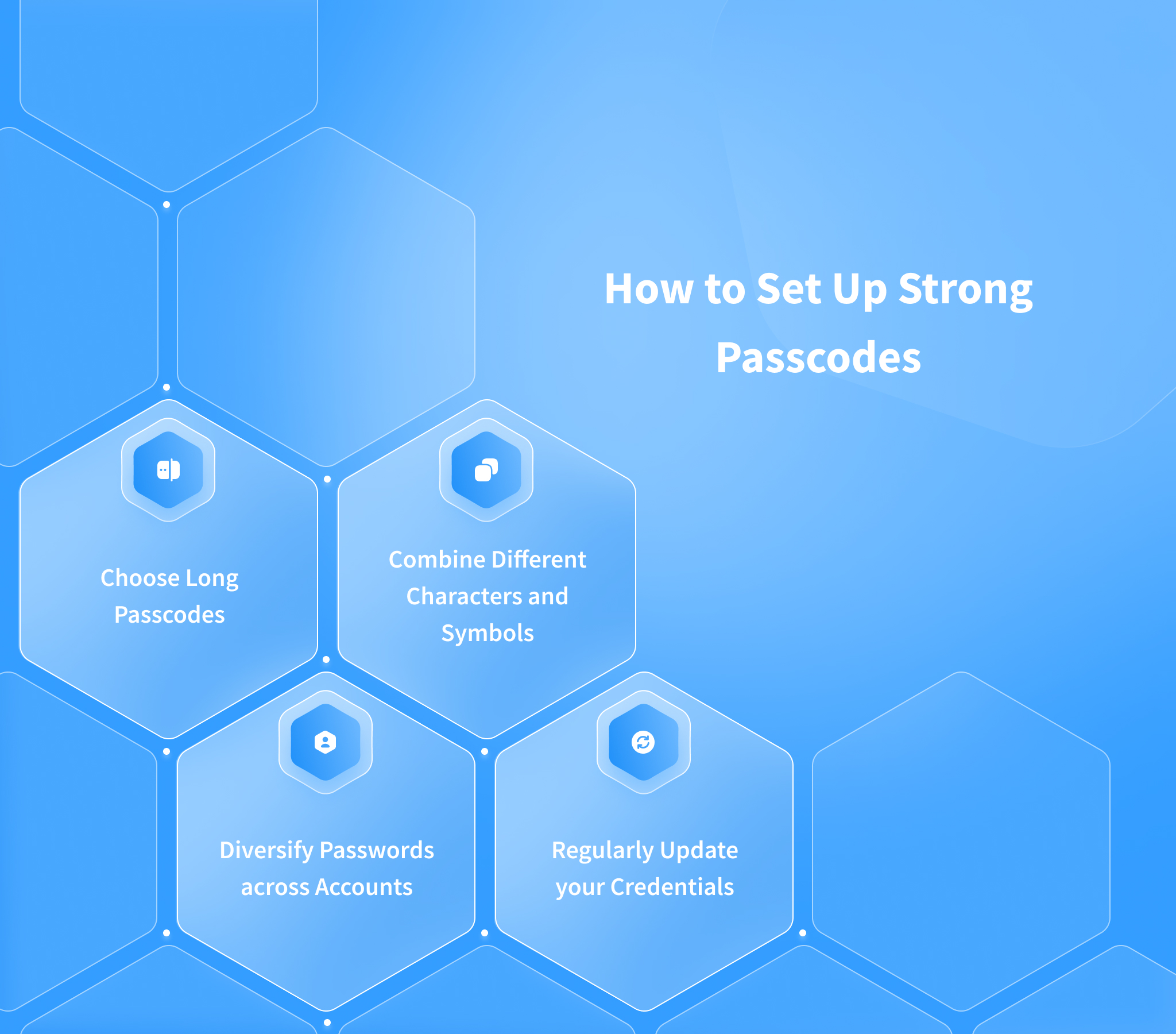
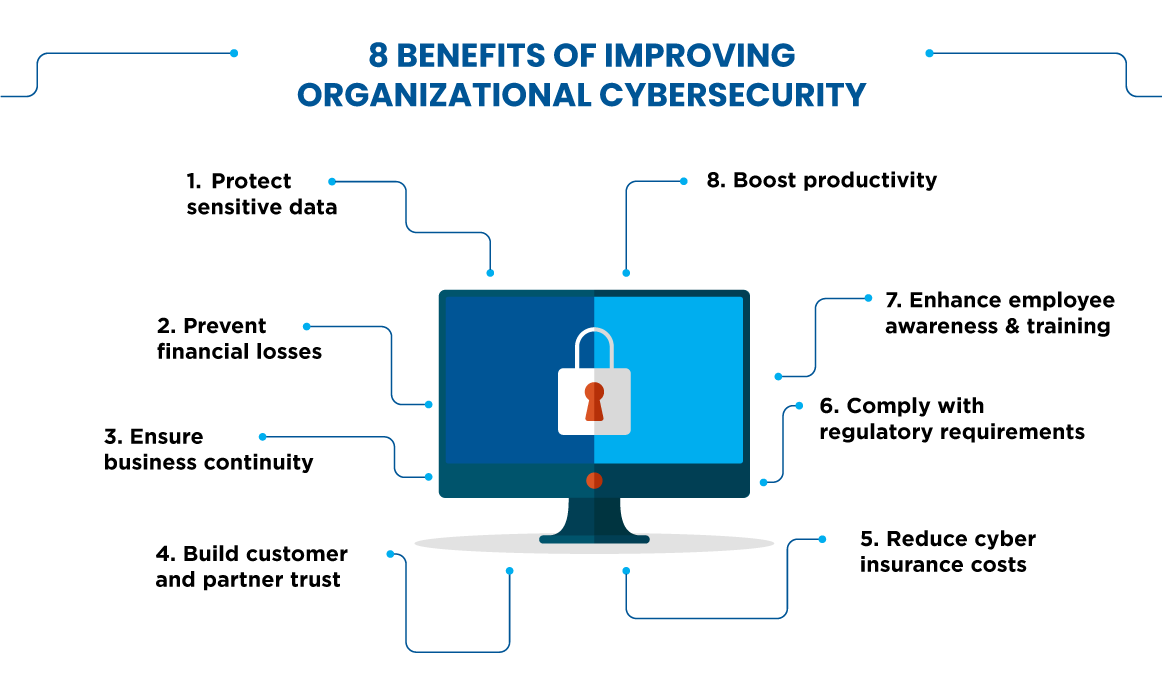
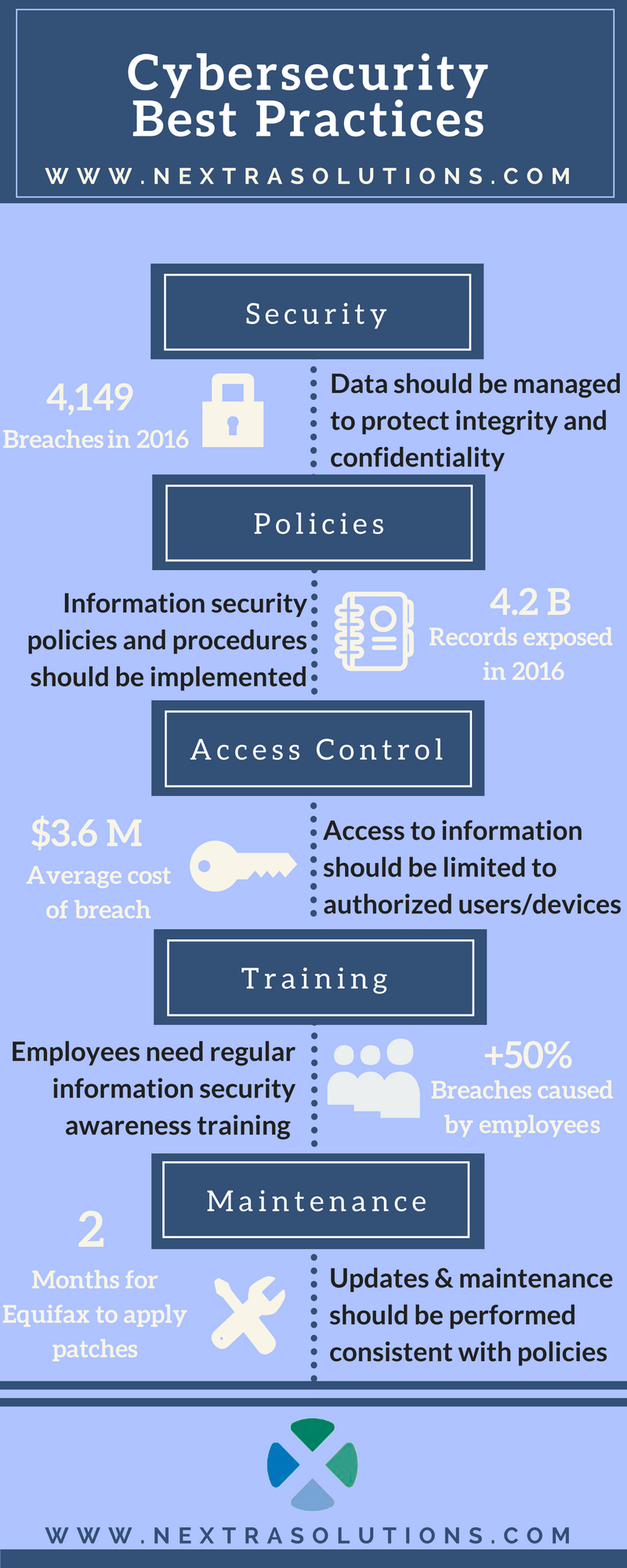
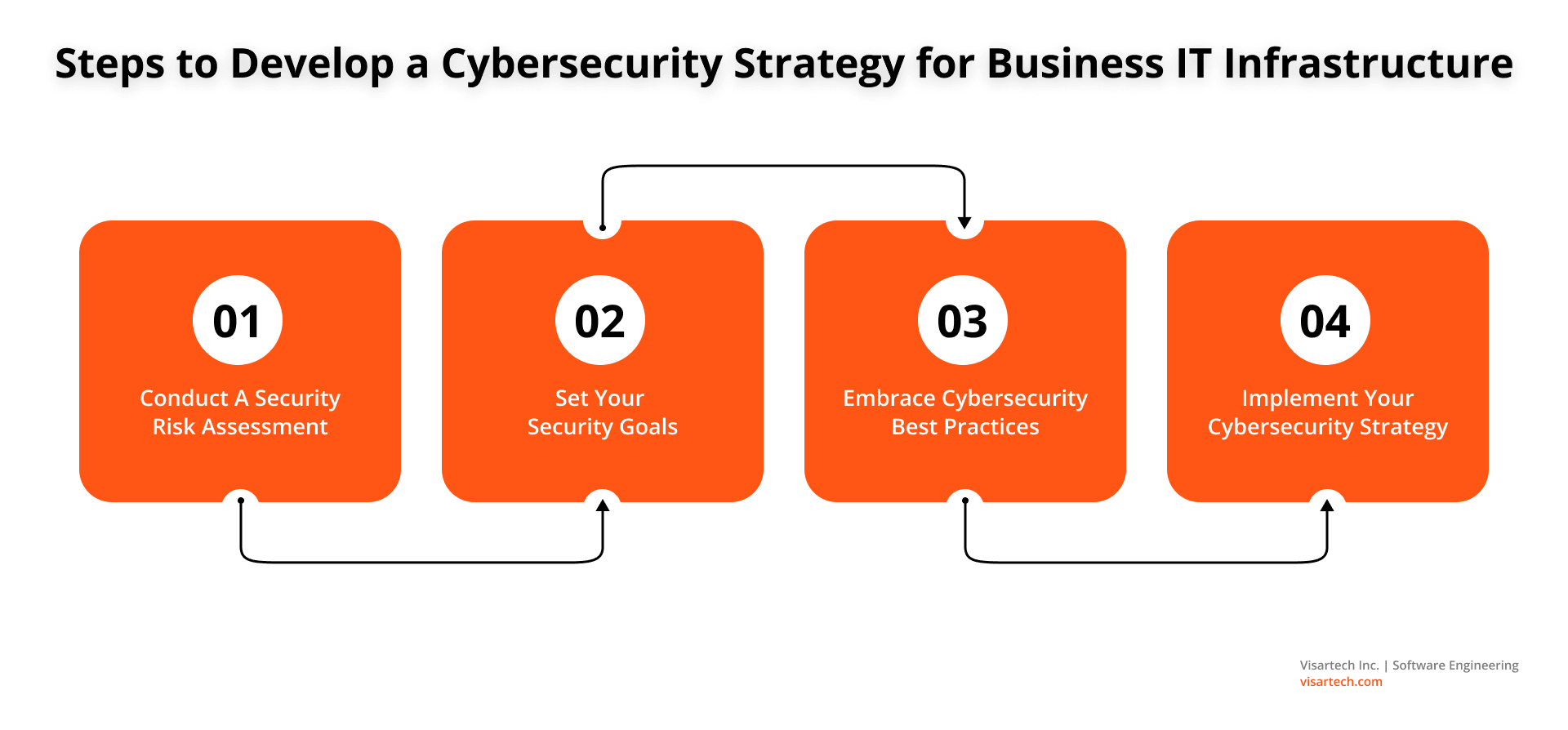
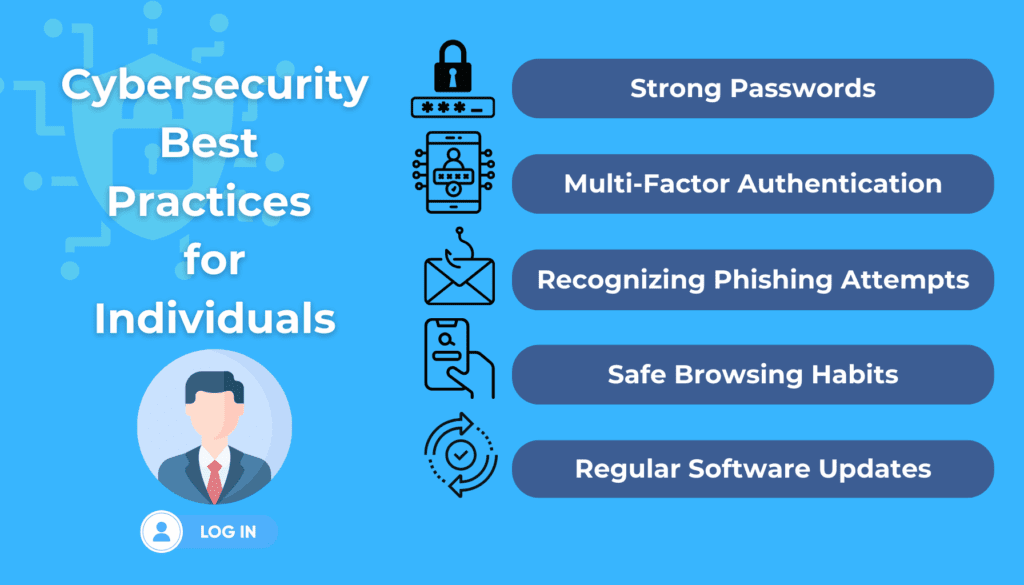
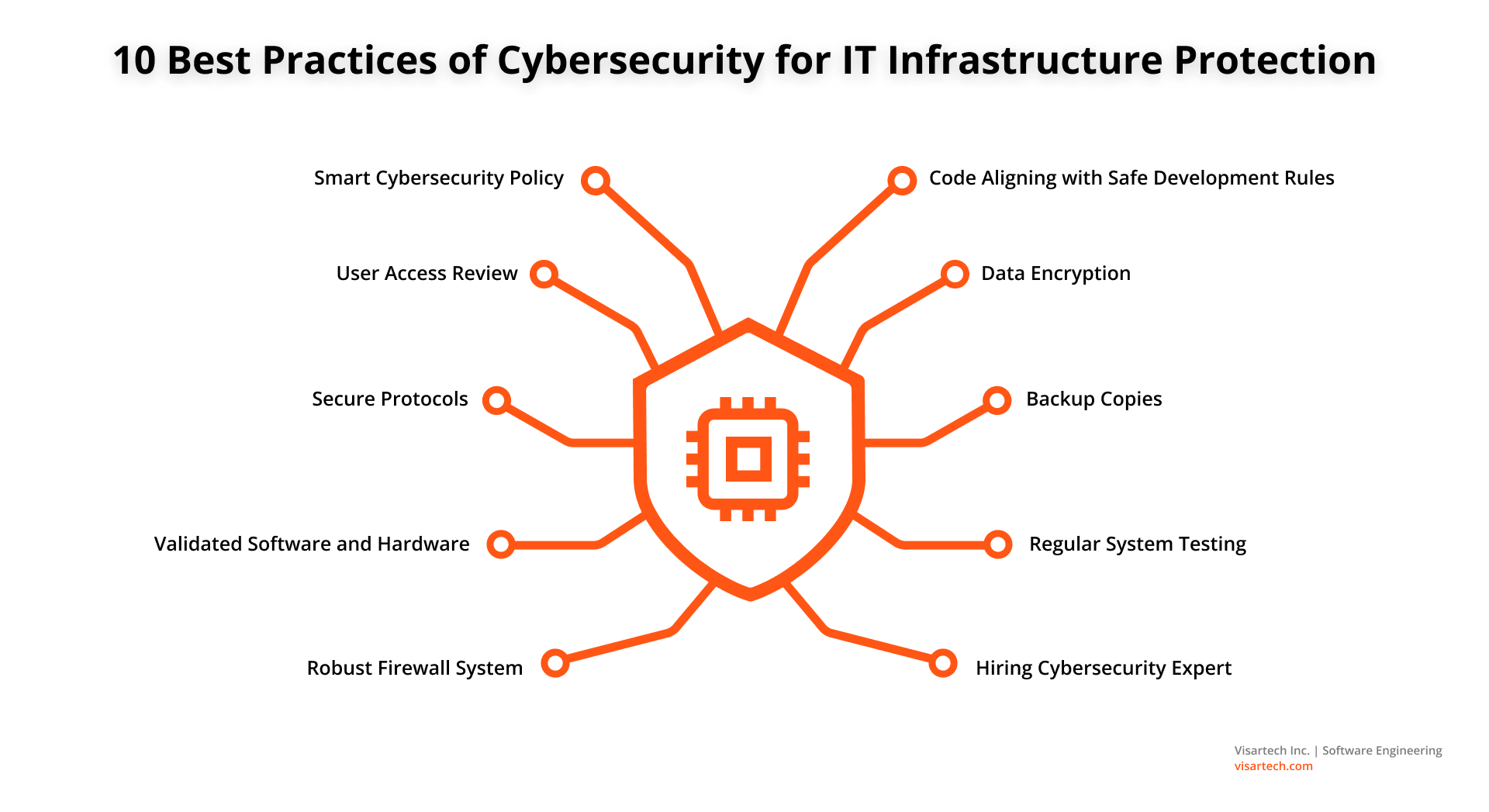
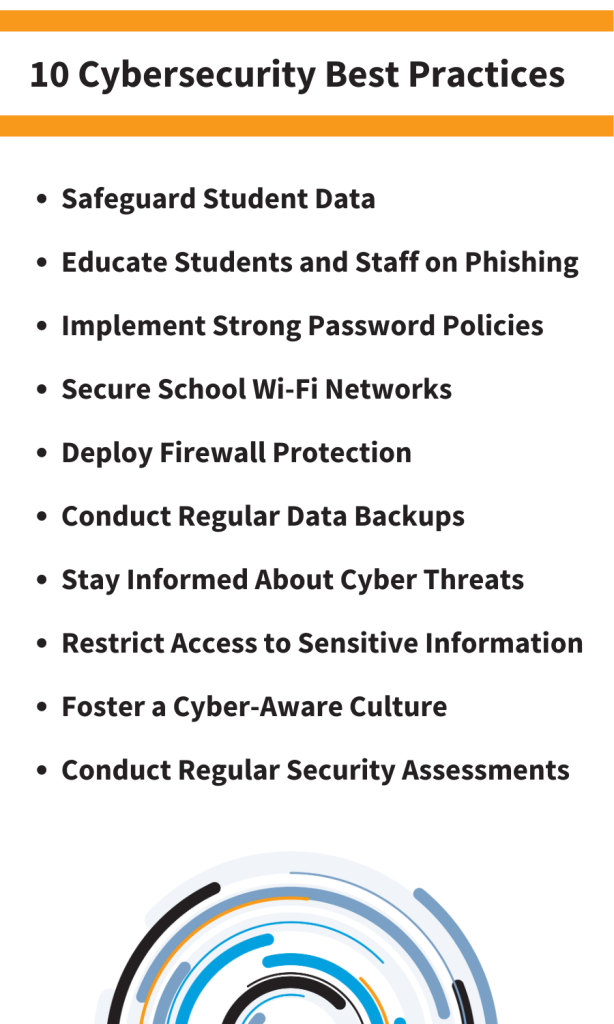
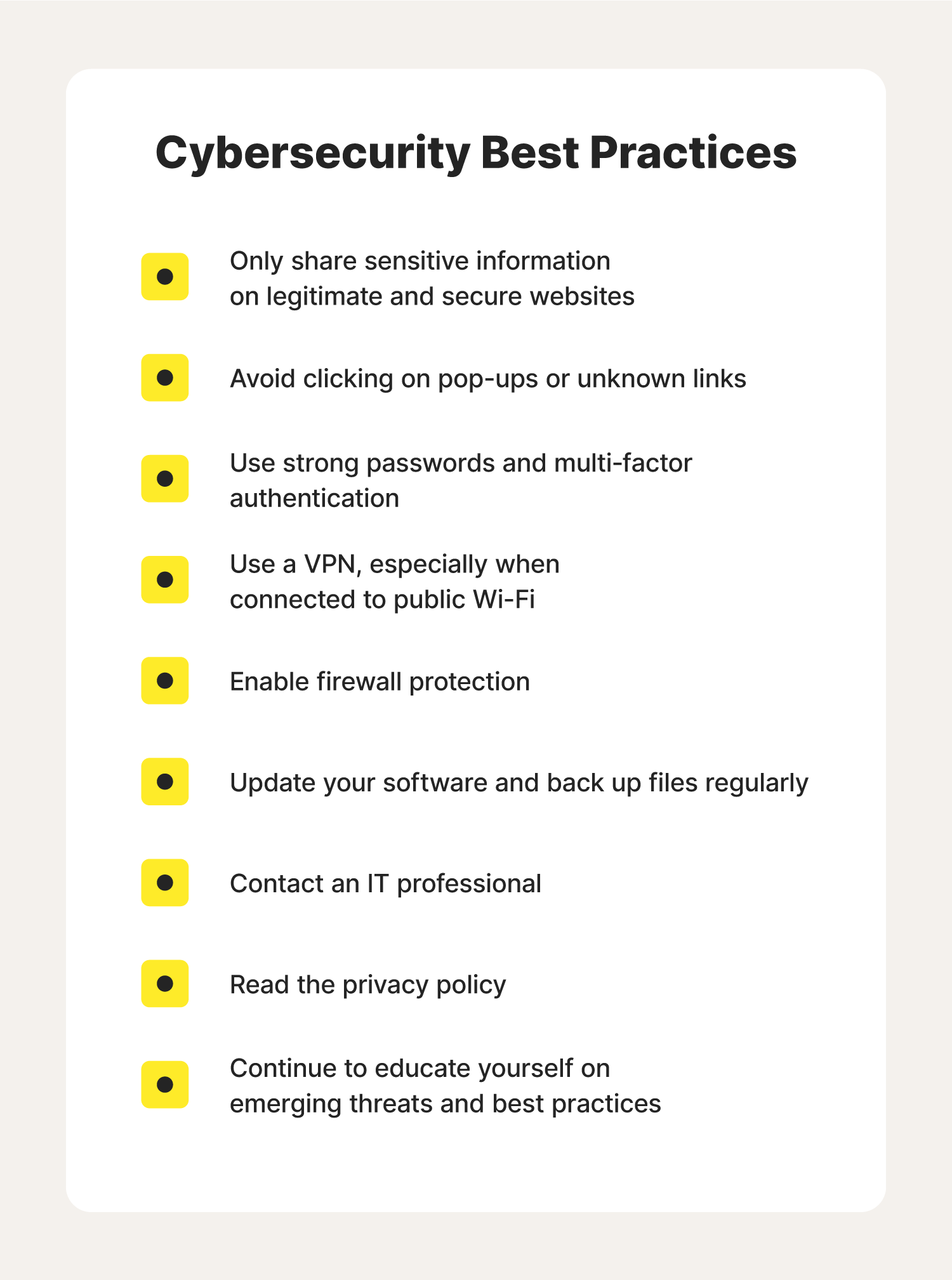
Here are some cybersecurity best practices for computer technology: Implement strong passwords and password management systems to prevent unauthorized access Use two-factor authentication (2FA) whenever possible to add an extra layer of security Keep software and operating systems up-to-date with the latest patches and updates Enable firewalls and intrusion detection systems to block suspicious network traffic Use encryption to protect sensitive data both in transit and at rest Restrict access to sensitive data and systems through role-based access control (RBAC) and least privilege principles Monitor system logs and security event management systems for potential security incidents Conduct regular vulnerability assessments and penetration testing to identify weaknesses Train employees on cybersecurity best practices and the importance of reporting suspicious activity
 Images
Images










































 Videos
Videos
















 Articles
Articles  Shopping
Shopping 


















 Media Sources
Media Sources 



















