 Definition
Definition
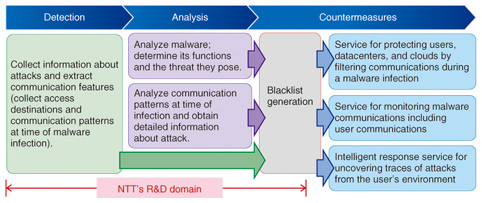
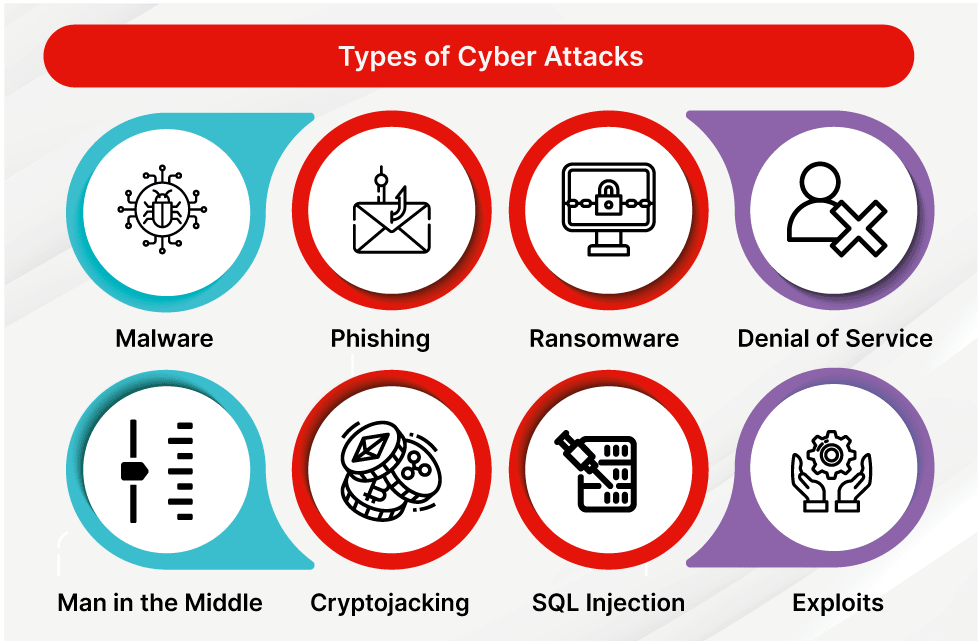
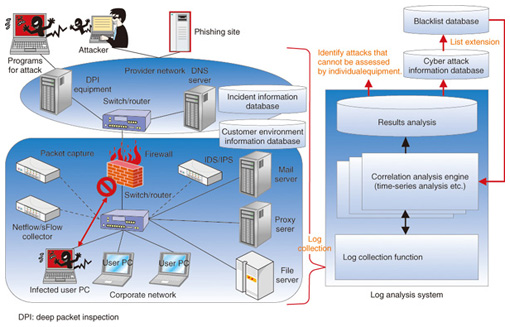
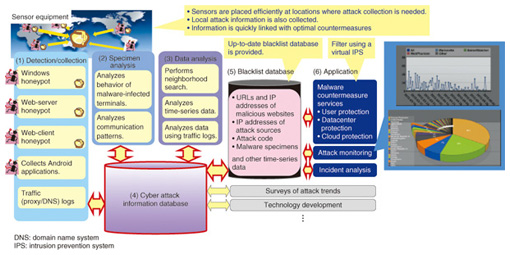
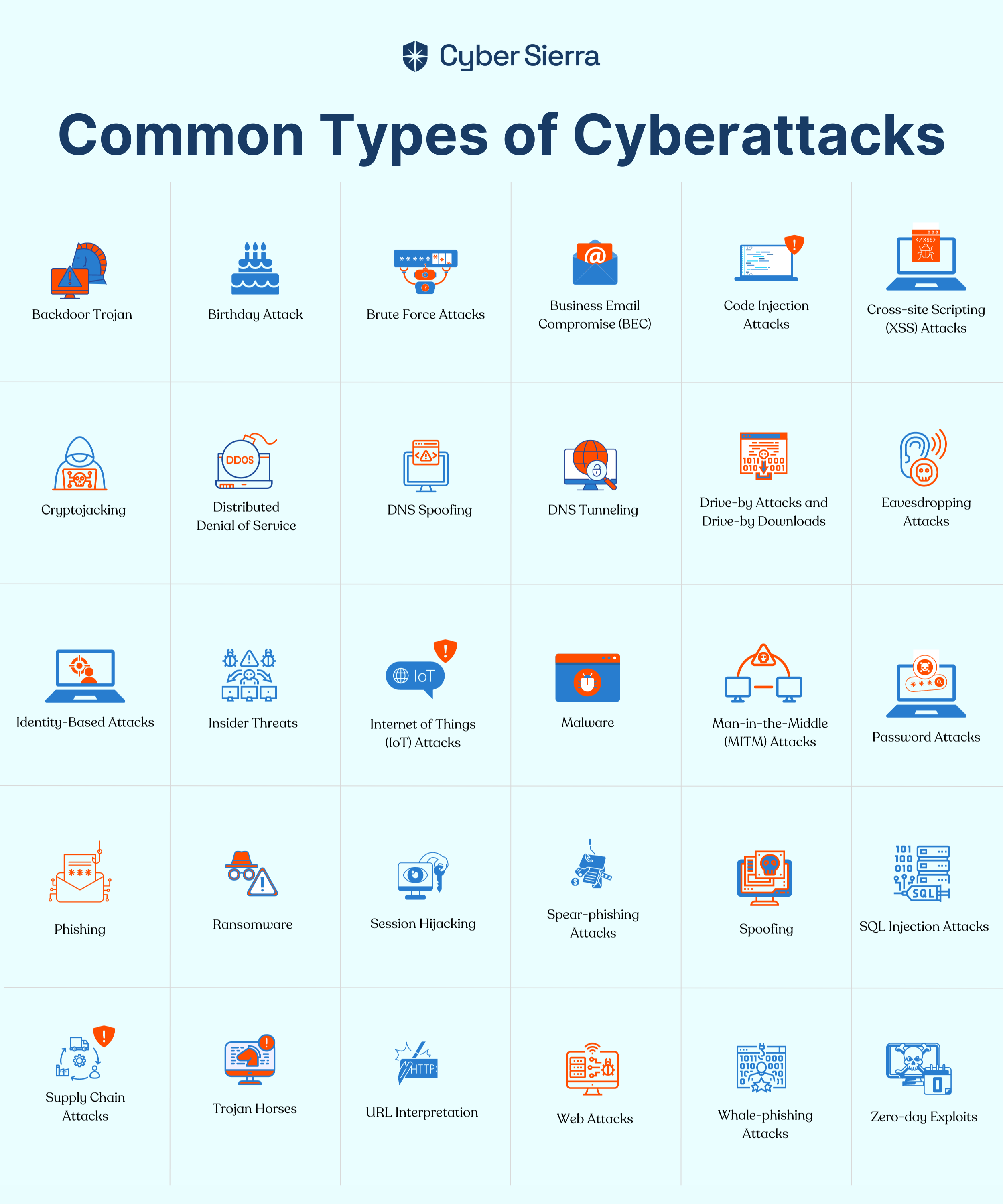
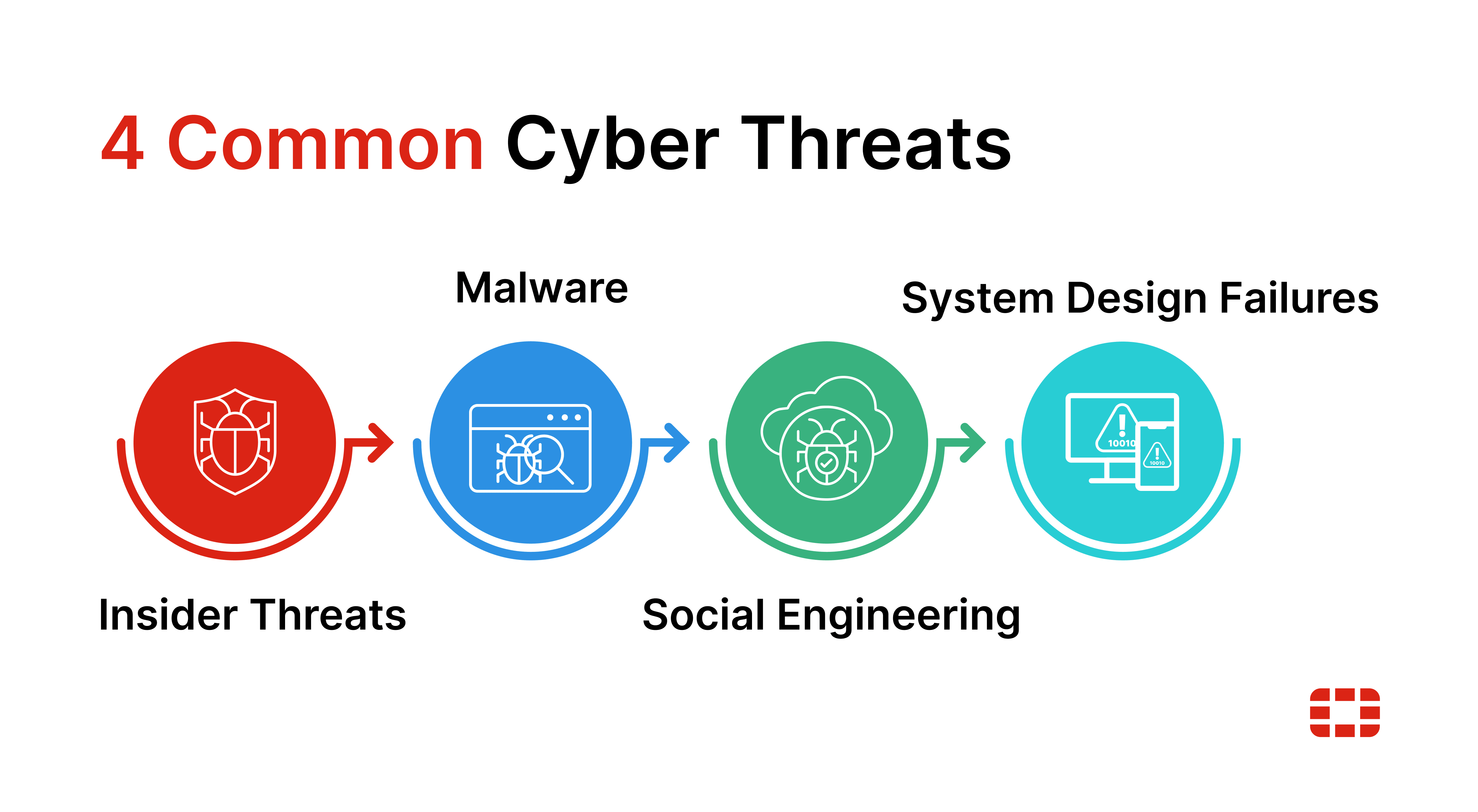
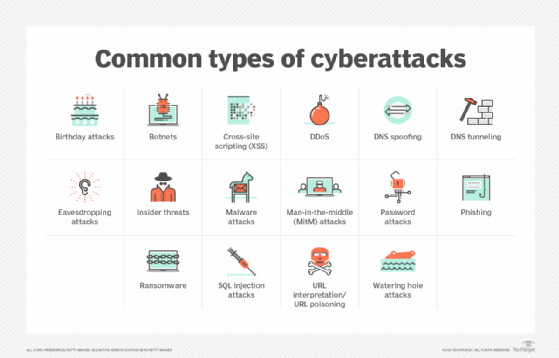
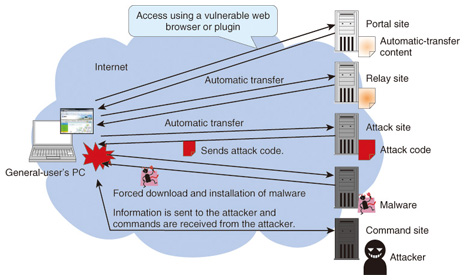
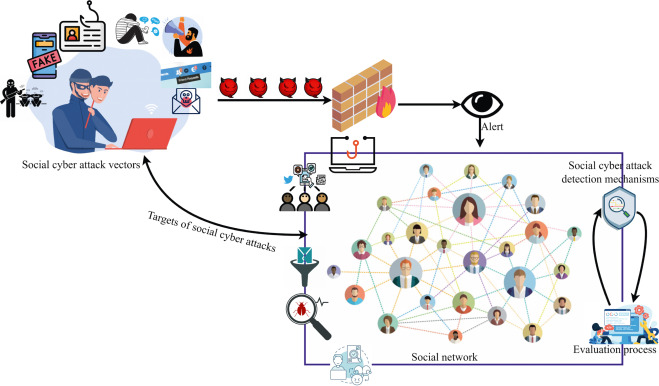
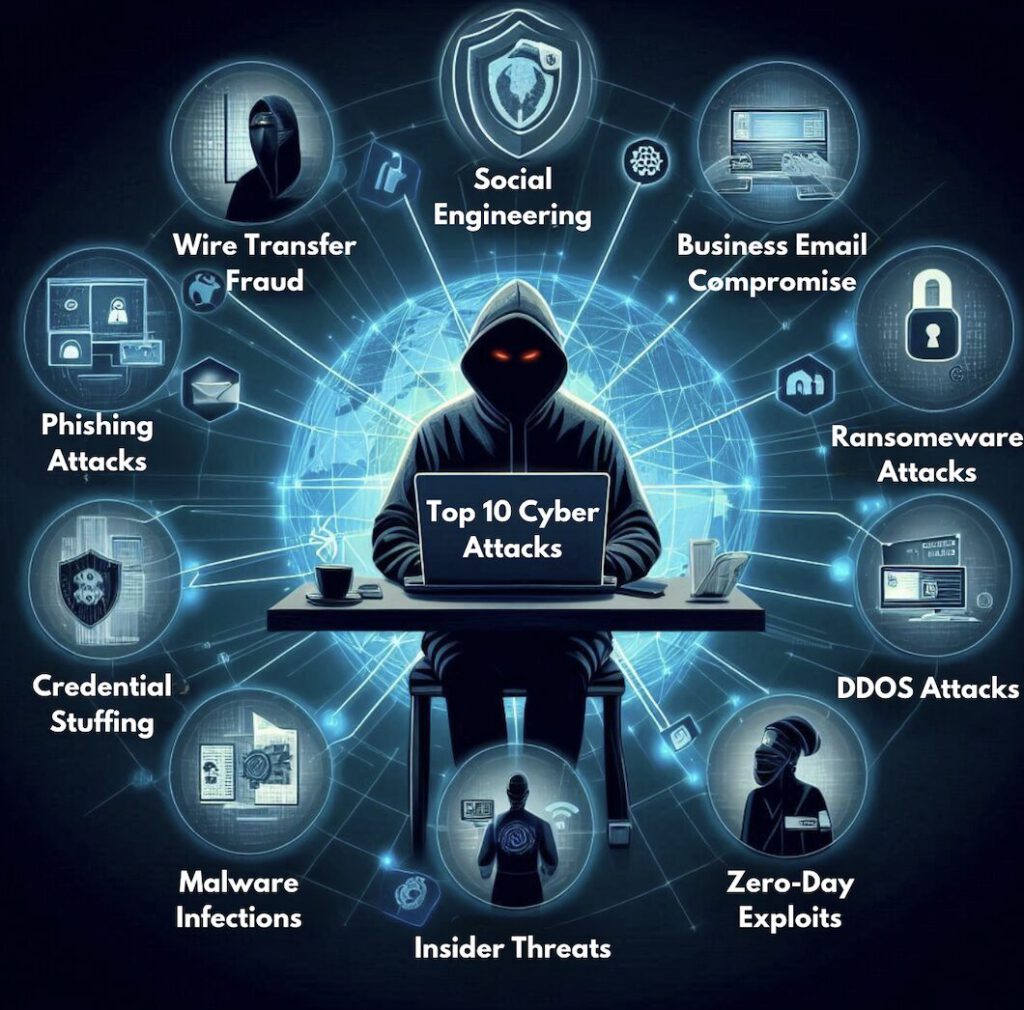
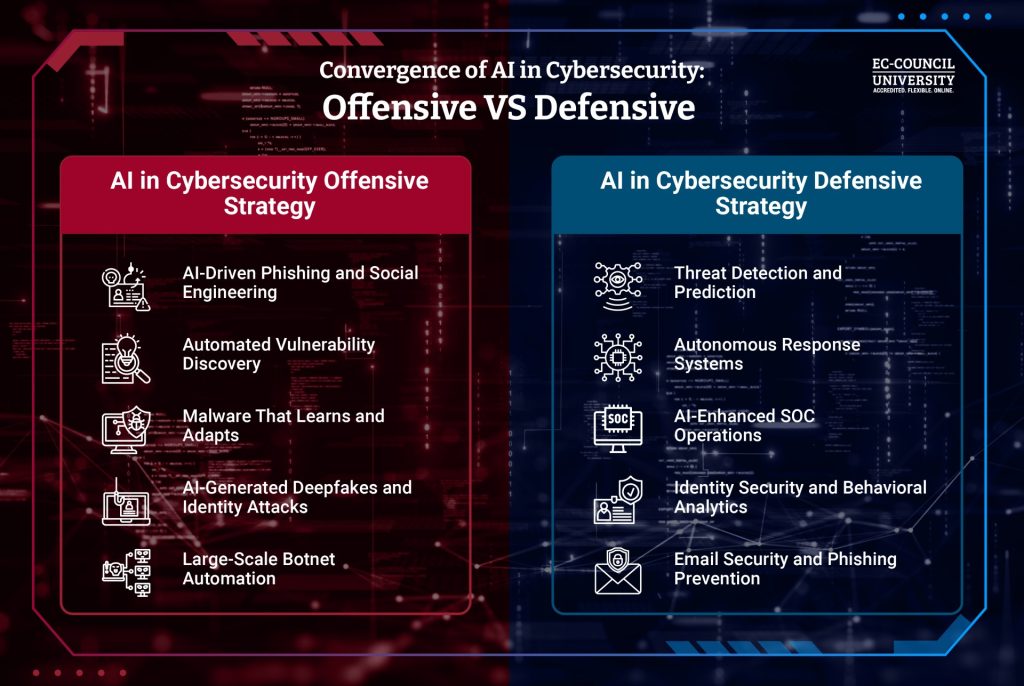
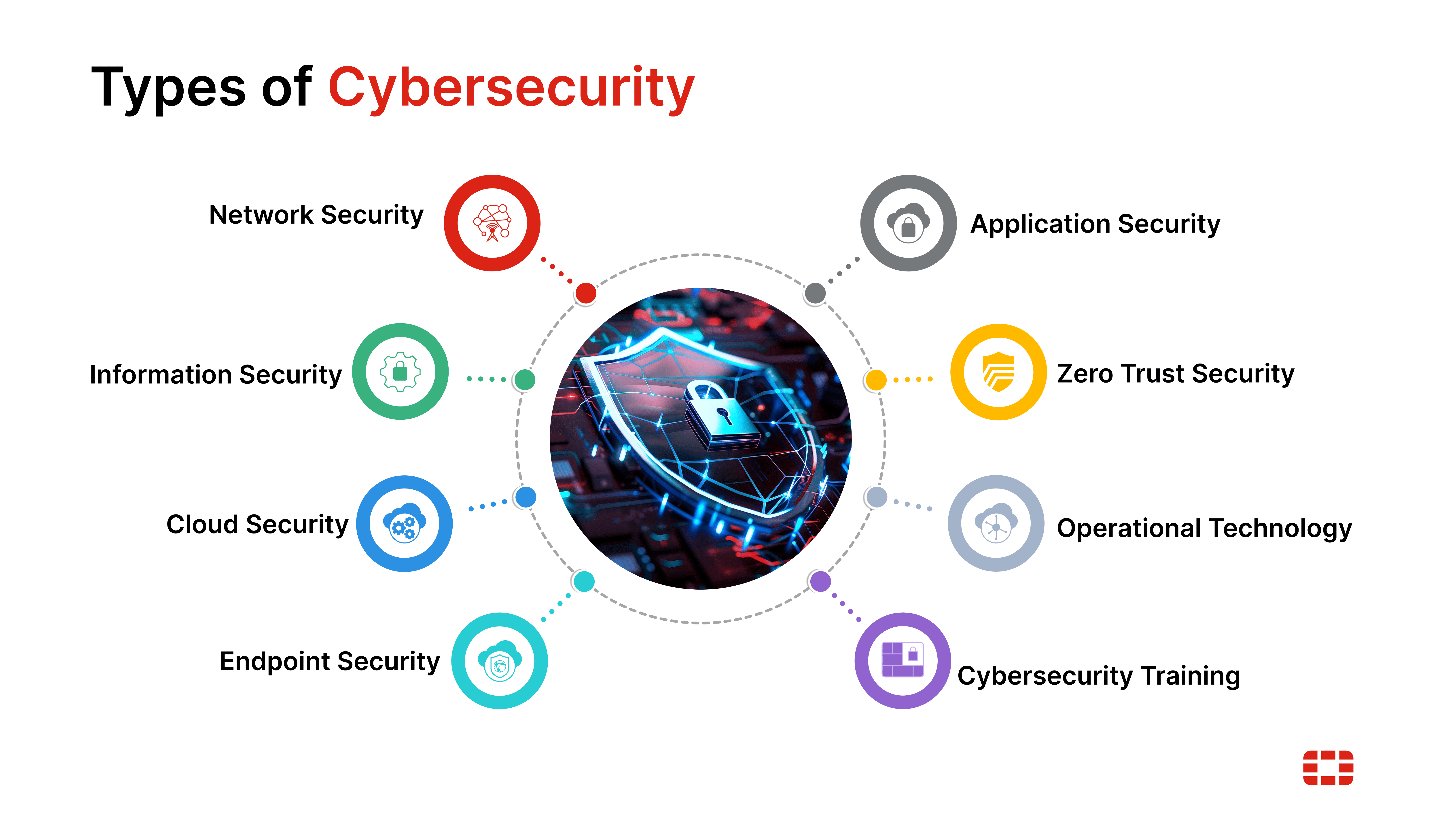
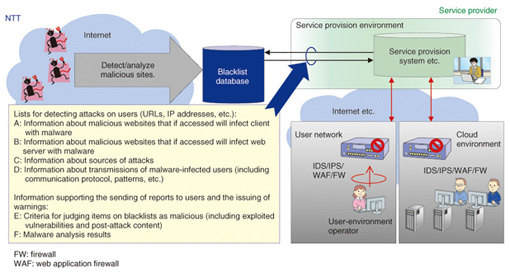
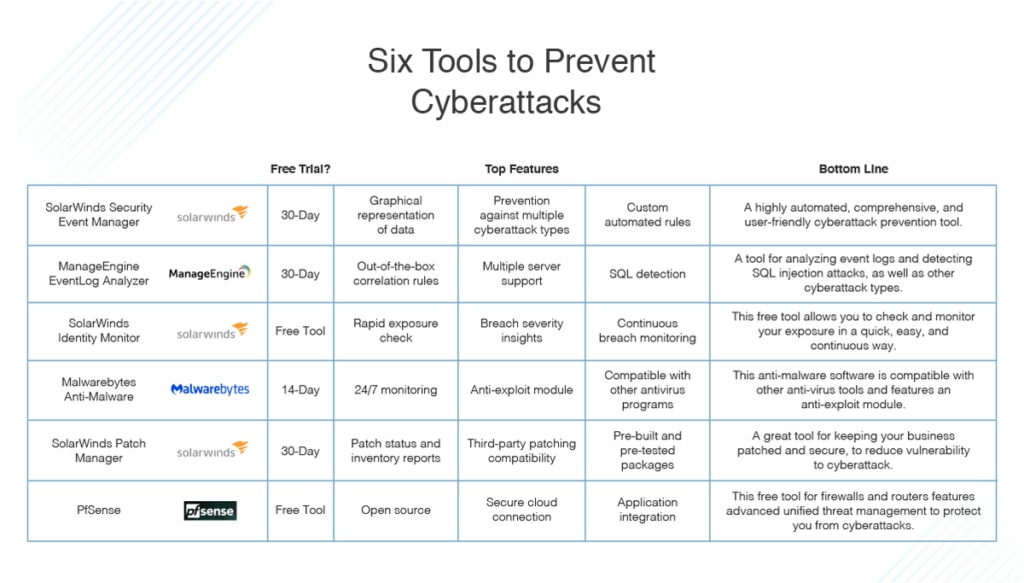
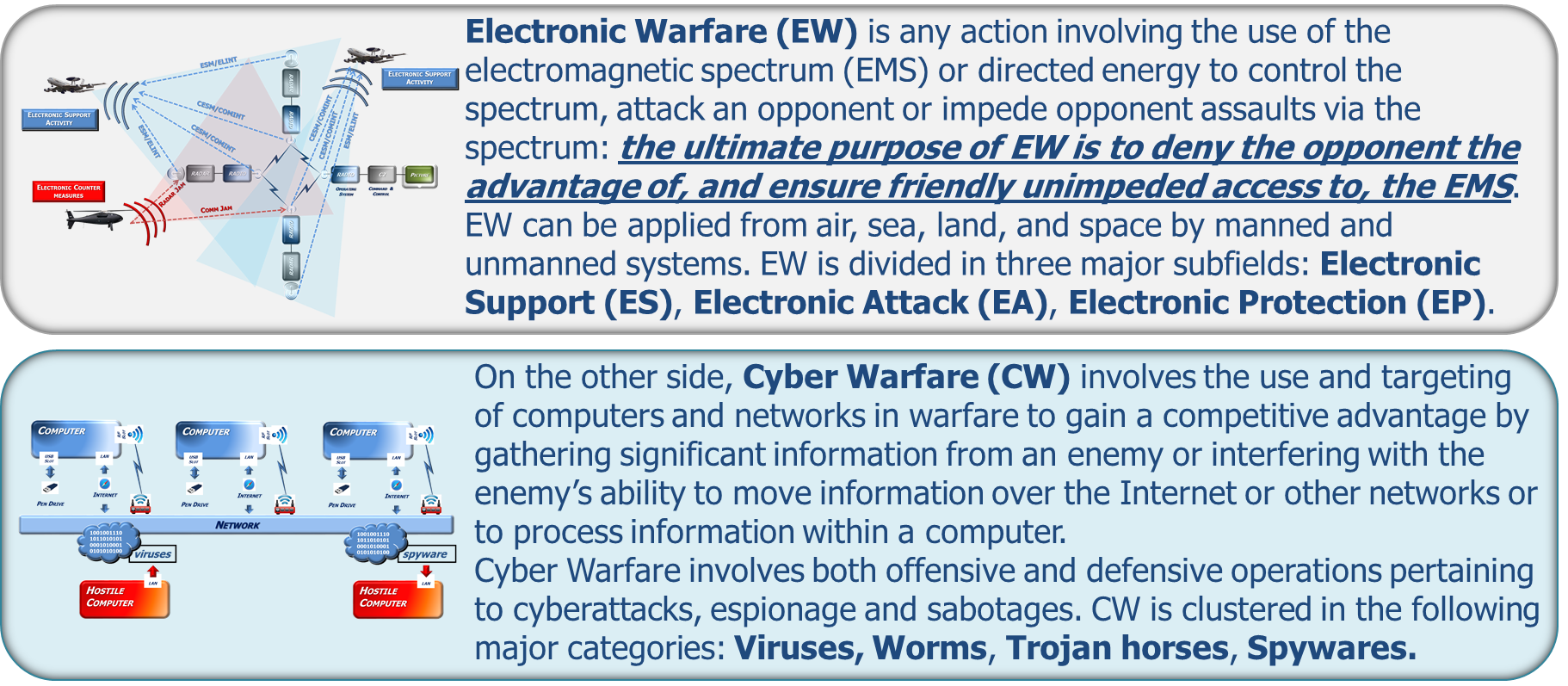
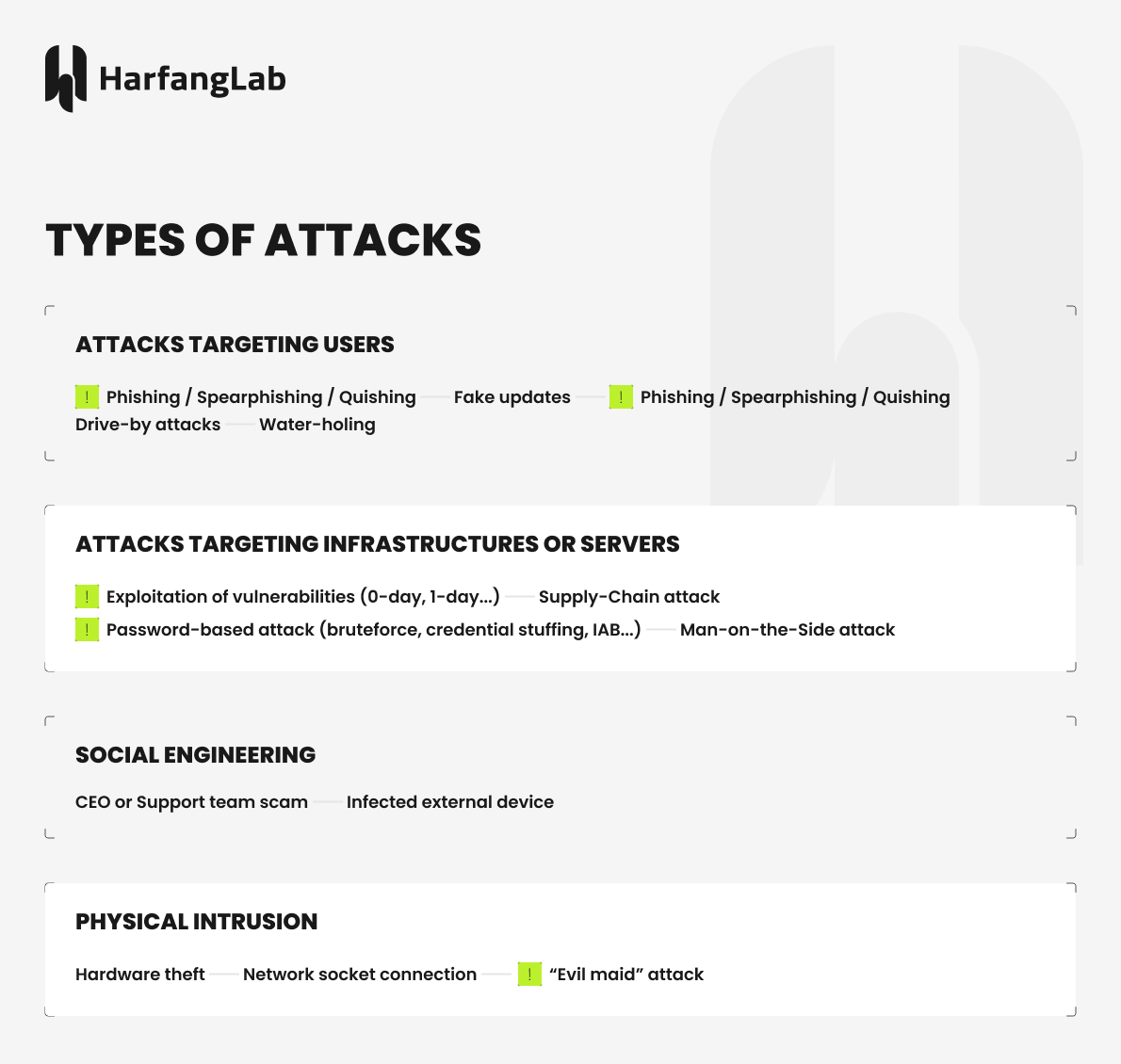
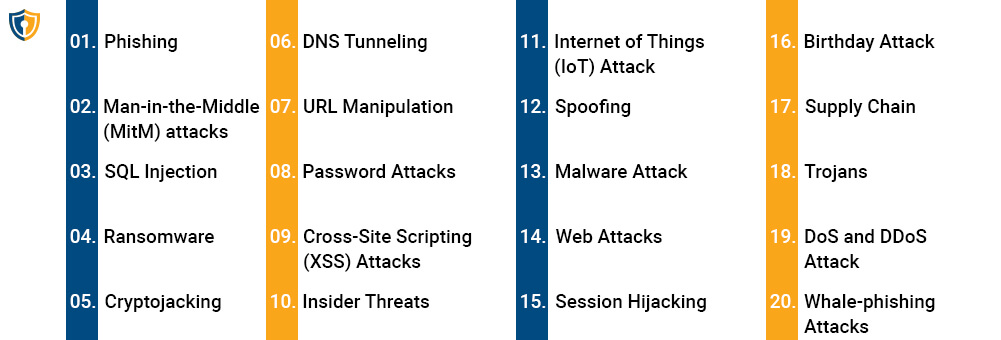
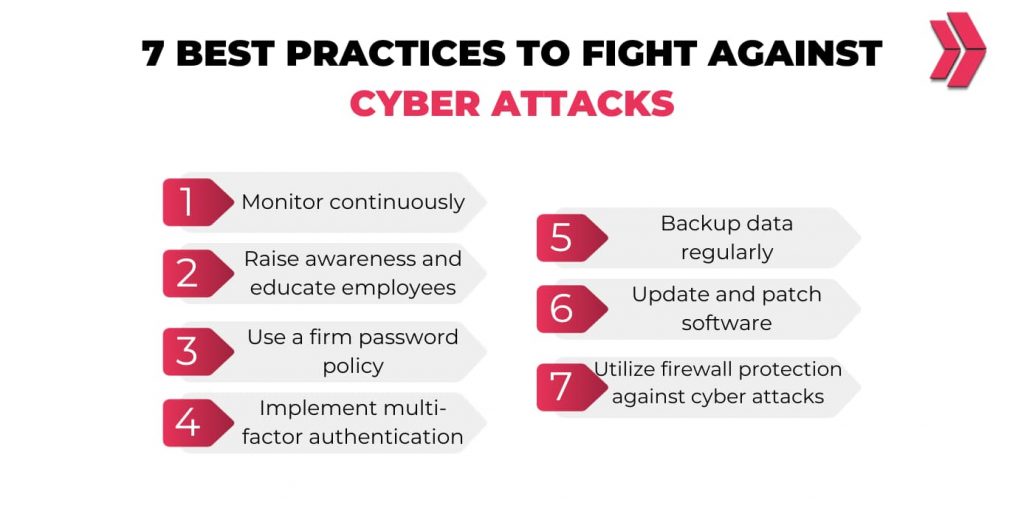
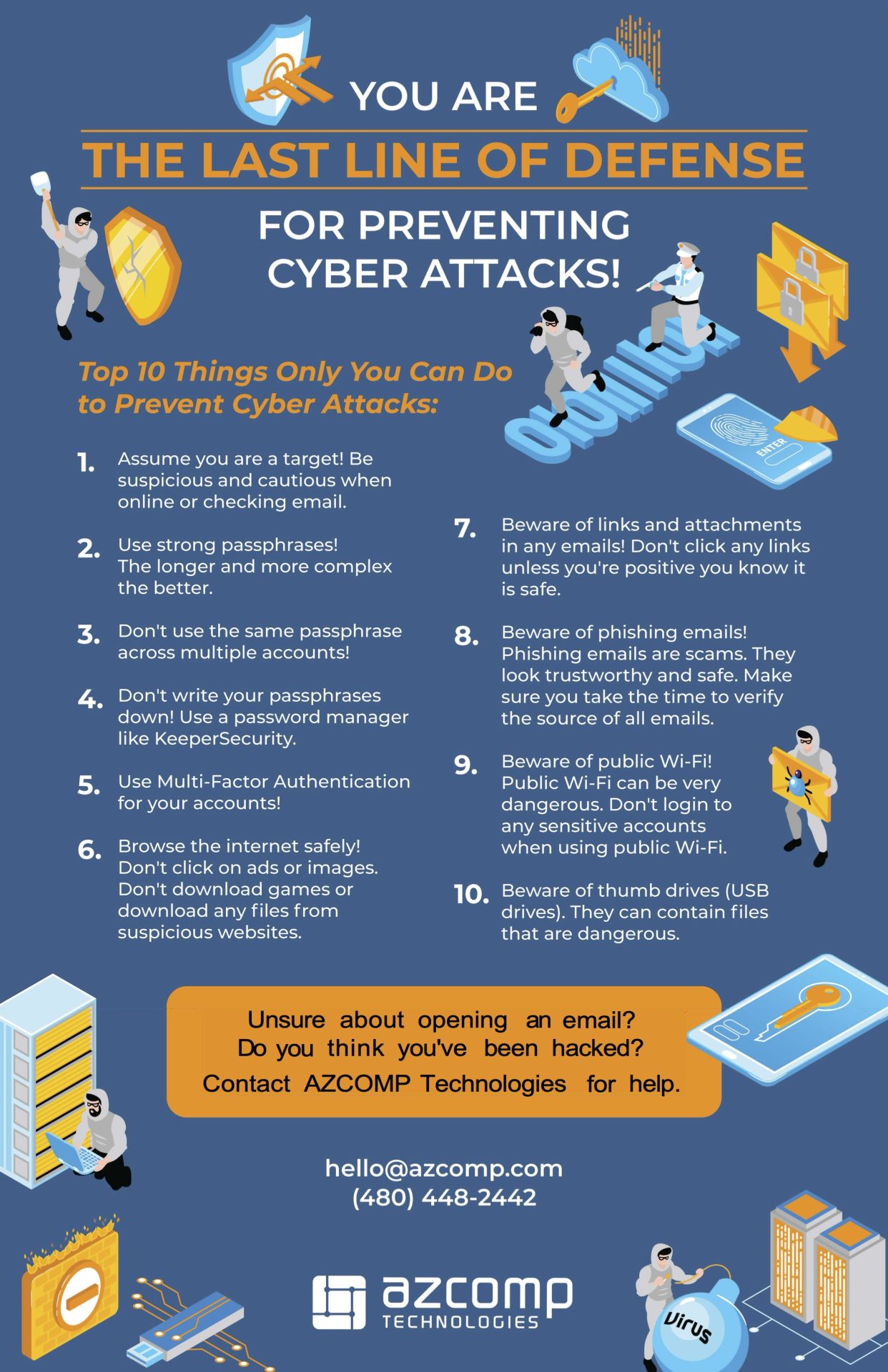
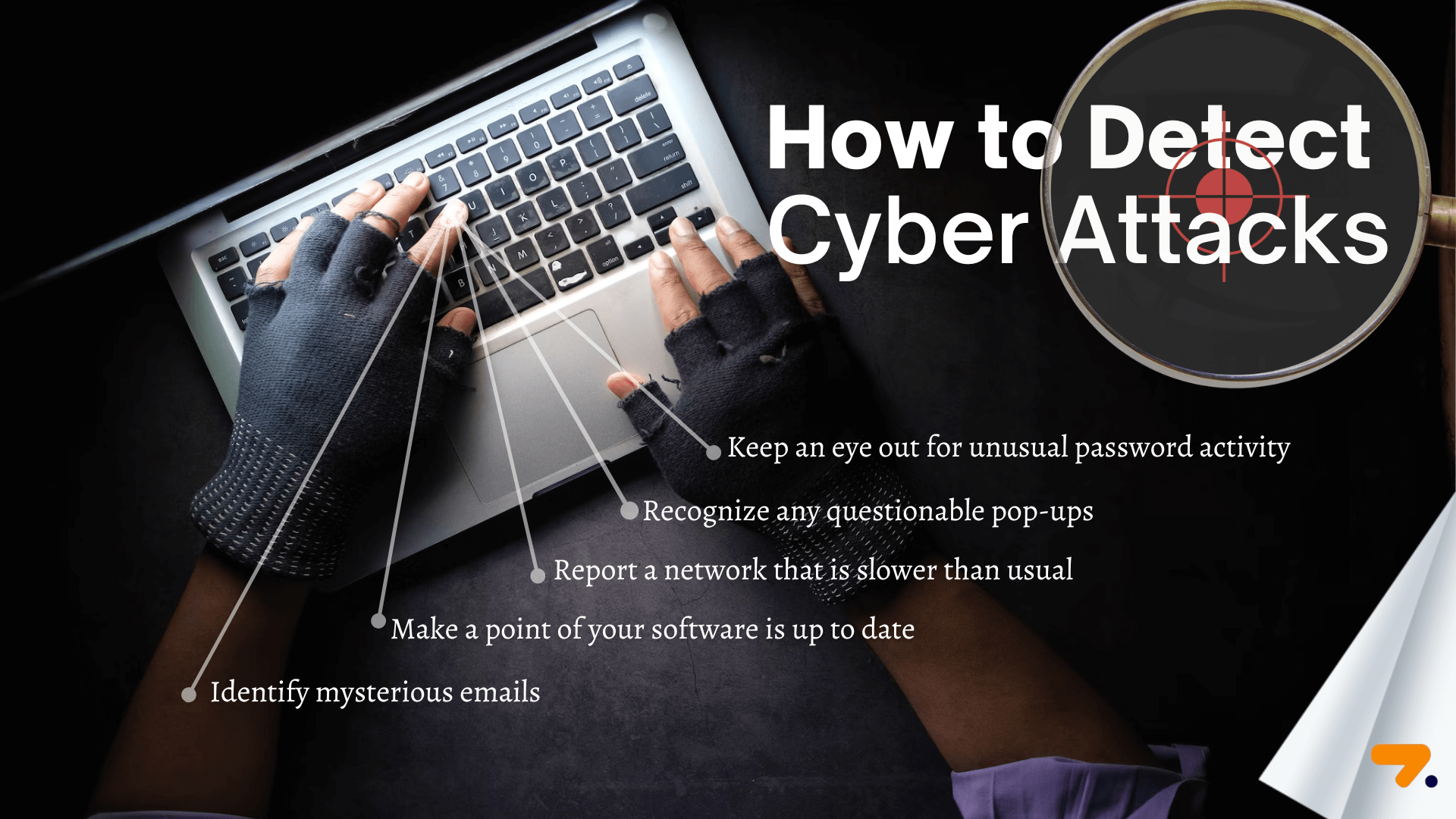
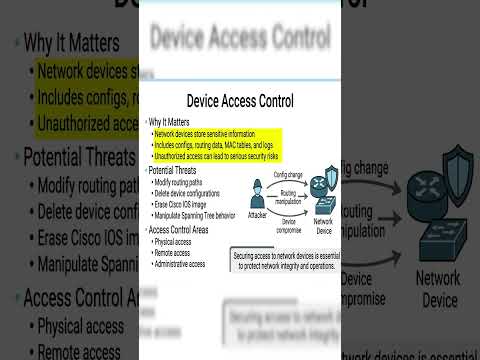
Cyber attacks refer to unauthorized access, disruption, modification, or destruction of computer systems and networks. Hackers use various techniques such as phishing, malware, and social engineering to gain access to sensitive information . Phishing involves sending fake emails or messages that trick users into revealing passwords or other confidential data . Malware includes viruses, worms, and Trojan horses that can corrupt or steal data, install backdoors, or take control of infected systems . Social engineering attacks manipulate individuals into divulging sensitive information or performing certain actions to compromise security . Firewalls and intrusion detection systems (IDS) provide network-based protection against cyber attacks by monitoring traffic for suspicious patterns . Encryption techniques scramble data making it unreadable without the decryption key, preventing unauthorized access or tampering . Secure coding practices and testing can help identify and fix vulnerabilities in software, reducing the risk of exploitable flaws . User awareness and education are crucial in preventing social engineering attacks by recognizing and reporting suspicious activities . Regular system backups, updates, and patches can minimize the impact of a successful cyber attack by quickly recovering from damage .
 Images
Images






















 Videos
Videos









 Articles
Articles  Shopping
Shopping 


















 Media Sources
Media Sources 



















